With the signing of America's Water Infrastructure Act (AWIA) into law in October 2018, the U.S. Environmental Protection Agency (EPA) is in the initial stages of providing risk and resiliency compliance guidance to community water systems.
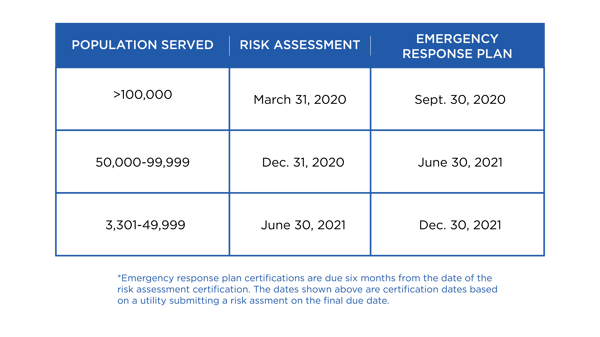
AWIA serves as an update to the Bioterrorism Act of 2002, which required water systems to conduct and develop vulnerability assessments and emergency response plans (ERPs). The AWIA also updates the risk and resiliency assessment (RRA) and ERP certification — and five-year recertification — requirements. EPA provides the following initial certification schedule for water systems:
 It is noteworthy that the EPA does not require community water systems to conduct new RRAs every five years, but to review their assessments and ERPs and recertify. It is the responsibility of water systems to conduct these assessments and update their ERPs as needed and in accordance with AWIA Section 2013 (a) and (b). For example, major infrastructure additions, renovations or changes in threat environments may trigger an update.
It is noteworthy that the EPA does not require community water systems to conduct new RRAs every five years, but to review their assessments and ERPs and recertify. It is the responsibility of water systems to conduct these assessments and update their ERPs as needed and in accordance with AWIA Section 2013 (a) and (b). For example, major infrastructure additions, renovations or changes in threat environments may trigger an update.
An additional advancement to the AWIA is the transition from a terrorism or intentional act vulnerability assessment approach to an “all-hazards” risk and resiliency assessment approach.
All-Hazards Approach
Specifically, the Act (Sec. 2013 Community Water System Risk and Resilience) states CWSs shall assess “... the risk to the system from malevolent acts and natural hazards; and the resilience of the pipes and constructed conveyances, physical barriers, source water, water distribution facilities, electronic, computer, or other automated systems (including the security of such systems) which are utilized by the system… ” From this language, we can interpret that a risk and resiliency all-hazards approach includes the assessment of the following components:
- Resiliency — the overall integrity and reliability (resiliency) of CWS sources and drinking water infrastructure against natural hazards (weather, natural disasters, life cycle, etc.)
- Cybersecurity — the identification of cybersecurity vulnerabilities to the CWS IT/OT networks and any associated financial management related systems (bill-pay, payroll, etc.)
- Physical security — how CWS sites are physically secured and adequately protected against acts of terrorism, malevolent acts and/or crimes of opportunity.
To assist community water systems with conducting risk and resiliency assessments, developing effective and actionable ERPs, and addressing an all-hazards assessment approach, the EPA will be releasing a Baseline Threat Document.
Often, the introduction of a law or regulation leaves an entity scrambling to obtain an understanding of how that regulation may affect it and how to successfully demonstrate compliance. Fortunately, most water systems should have what is required by the AWIA already in motion as a result of the Bioterrorism Act of 2002, including internal ERPs. Water providers are now tasked with taking a comprehensive assessment of multiple system components and updating their existing ERPs, which ideally should already be incorporated into the security/risk management program.
Evolving Threat Environments
If anything is certain, it is that threat environments are continually changing. Traditional crimes of opportunity like theft and vandalism are evolving to acts of terrorism or lone wolf attacks where an adversary’s objective is to generate panic and not necessarily cause destruction. The wave of automation has influenced the connection of utility monitoring systems into the Internet of Things (IoT), ultimately resulting in sophisticated and costly cybersecurity vulnerabilities.
Due to the overall nationwide impact, U.S. critical infrastructure utilities, including water systems, are at the forefront of this change.
In parallel, the electric industry is no stranger to evolving threat environments and regulatory guidance. In 2013, a malevolent attack on a large substation resulted in more than $15 million in damage and the introduction of the North American Electric Reliability Corp. standards for Critical Infrastructure Protection (NERC-CIP 014-2).
These NERC CIP standards require electric utilities to conduct physical security evaluations on critical substations and establish physical security plans. Somewhat reflective of these standards, the AWIA not only addresses physical security but also outlines an all-hazards approach to protecting against the evolving natural and malevolent threat environment specific to the water industry.
AWIA sets into motion a timeline for risk and resiliency compliance requirements for community water systems. A cohesive, comprehensive approach that incorporates best practices for infrastructure resiliency, physical security and cybersecurity can keep you ahead of fast-approaching compliance deadlines.

